Which configuration shows the correct application of a security policy scheduler?()
第1题:
A.dumpctrl
B.sysdumpdev
C.livedumpdev
D.livedumpctrl
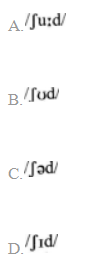
第2题:
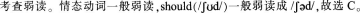
第3题:

A.It shows the total size of the index row
B.It shows how many columns in the index are examined
C.It shows the number of characters indexed in the key
D.It shows how many bytes will be used from each index row
第4题:
An engineer has added the following configuration snippet to an implementation planning document. The configuration will be added to Router R1, whose Fa0/0 interface connects to a LAN to which Routers R2 and R3 also connect. R2 and R3 are already EIGRP neighbors with each of her. Assuming the snippet shows all commands on R1 related to EIGRP authentication, which answer lists an appropriate comment to be made during the implementation plan peer review?() key chain fred key 3 key - string whehew interface fa0/0 ip authenticat ion key - chain eigrp 9 fred
第5题:

第6题:
A. It is a globally unique IP address.
B. It is a globally unique 48 bit address
C. It is provided by the manufacturer of the NIC.
D. It is used as part of the IPX/SPX configuration.
E. It is a logical address.
第7题:

第8题:
You have been asked to configure a login class which will permit its users to view and edit the configuration. The class should only allow the configuration of the interfaces and firewall heirarchies. Which configuration correctly accomplishes this?()

A.A
B.B
C.C
D.D
第9题:
第10题:
Which CLI mode allows you to make configuration changes?()